Access control acts as the bedrock of any robust security system. By meticulously deploying access control policies, organizations can reduce the risk of unauthorized incursion to sensitive data and systems. It enables the precise management of user authorizations, ensuring that individuals only are granted access to the resources required for their roles.
A well-defined access control strategy empowers organizations to comply with regulatory requirements and preserve their crucial assets from malicious threats.
Demystifying Access Control Systems
Access control systems can seem like a complex and intimidating technology, however, the fundamental principles are surprisingly straightforward. These systems are designed to restricting access to resources based on user identities.
Many types of access control systems available, each with its own benefits and weaknesses. Typical examples include card readers, which use physical identification to verify users.
Other systems implement digital tools to regulate access. This can comprise firewalls, intrusion detection systems, and permission-based access controls.
Understanding the numerous types of access control systems and their purposes is essential for securing sensitive information and assets.
Navigating the Landscape: Types of Access Control in Security
Securing valuable information is paramount in today's digital landscape. Access control plays a critical role in this endeavor, determining who can access what systems and data. Understanding the various types of access control is essential for implementing robust security measures.
- Role-based Access Control (RBAC): This approach grants permissions based on a user's positions within an organization.
- Rule-based Access Control (MAC/DAC/RAC): MAC imposes strict security policies, while DAC allows users to control access to their own resources. RAC combines aspects of both approaches.
- Layered Authentication: This method requires users to provide multiple forms of identification, enhancing security by reducing the risk of unauthorized access.
Choosing the right type(s) of access control depends on factors such as organizational sensitivity and regulatory requirements. By carefully analyzing these factors, organizations can create a layered security framework that effectively protects their valuable assets.
Strengthening Defenses: 5 Critical Access Control Techniques
In today's read more cybersecurity landscape, protecting your perimeter is paramount. A robust access control system acts as the first line of defense, limiting unauthorized access to your resources. Implementing effective access control methods can substantially reduce the risk of breaches and security incidents.
- One crucial method is enhanced authentication, which requires users to provide multiple forms of identification before gaining access.
- Fingerprint scanning uses unique biological traits to identify user identity, offering a high level of safeguarding.
- Role-based access control (RBAC) define specific permissions for different users or groups, ensuring that individuals only have access to the information they need.
- Network monitoring solutions constantly analyze network traffic for suspicious activity, providing real-time notifications of potential threats.
- Penetration testing help identify weaknesses in your access control system and provide recommendations for strengthening.
By implementing these essential access control methods, you can effectively secure your perimeter and create a more resilient security posture.
System Permissions: A Deep Dive into System Configurations
Access control mechanisms are fundamental to safeguarding critical assets. A robust access control system ensures that only authorized individuals can utilize specific resources. This requires meticulous system parameters to define user roles, privileges, and access tiers.
Well-defined access control policies are indispensable for mitigating cyber vulnerabilities. These standards precisely define the extent of user authorizations based on their roles and responsibilities.
To achieve a secure infrastructure, administrators must configure a multi-layered access control framework. This may include techniques such as:
* User Verification:
Verifying the authorization of users attempting to gain entry to a system.
* Access Control Enforcement: Determining which systems authorized users can utilize.
* Auditing:
Tracking and analyzing user activity to detect potential security breaches.
Regularly reviewing access control configurations is crucial for maintaining a secure system. As business requirements change, access control strategies must be updated accordingly to ensure continued security.
Implementing Effective Access Control Strategies
Securing your network is paramount in today's digital landscape. A robust framework for access control is essential to reduce unauthorized access and potential breaches. Effective access control involves a multi-layered approach that encompasses verification mechanisms, authorization policies, and ongoing monitoring. By establishing these safeguards, organizations can control user permissions based on their roles and responsibilities, thereby ensuring that only authorized individuals can access sensitive information and resources.
- Determine clear roles for users.
- Implement strong verification methods, such as multi-factor verification.
- Periodically review access controls to uncover any potential vulnerabilities.
 Emilio Estevez Then & Now!
Emilio Estevez Then & Now!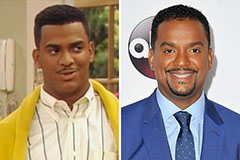 Alfonso Ribeiro Then & Now!
Alfonso Ribeiro Then & Now! Josh Saviano Then & Now!
Josh Saviano Then & Now! Kane Then & Now!
Kane Then & Now! Nadia Bjorlin Then & Now!
Nadia Bjorlin Then & Now!